The Equifax Catastrophe: How One Missed Update Became a $700M Fine In most workplaces, ...
In most workplaces, it’s common to delay non-urgent updates. A message comes in—on email, Teams, or chat—and gets pushed to “later.” Most of the time, nothing happens.
But in 2017, that “later” moment at Equifax turned into one of the largest data breaches in history.
What Equifax does
Equifax is one of the three major U.S. credit bureaus. It stores and analyzes highly sensitive financial data used for credit checks, loans, identity verification, and fraud prevention.
This makes it a critical part of the global financial system.
Tired of reminding staff to read your company policies?
DocRead makes compliance simple
What went wrong
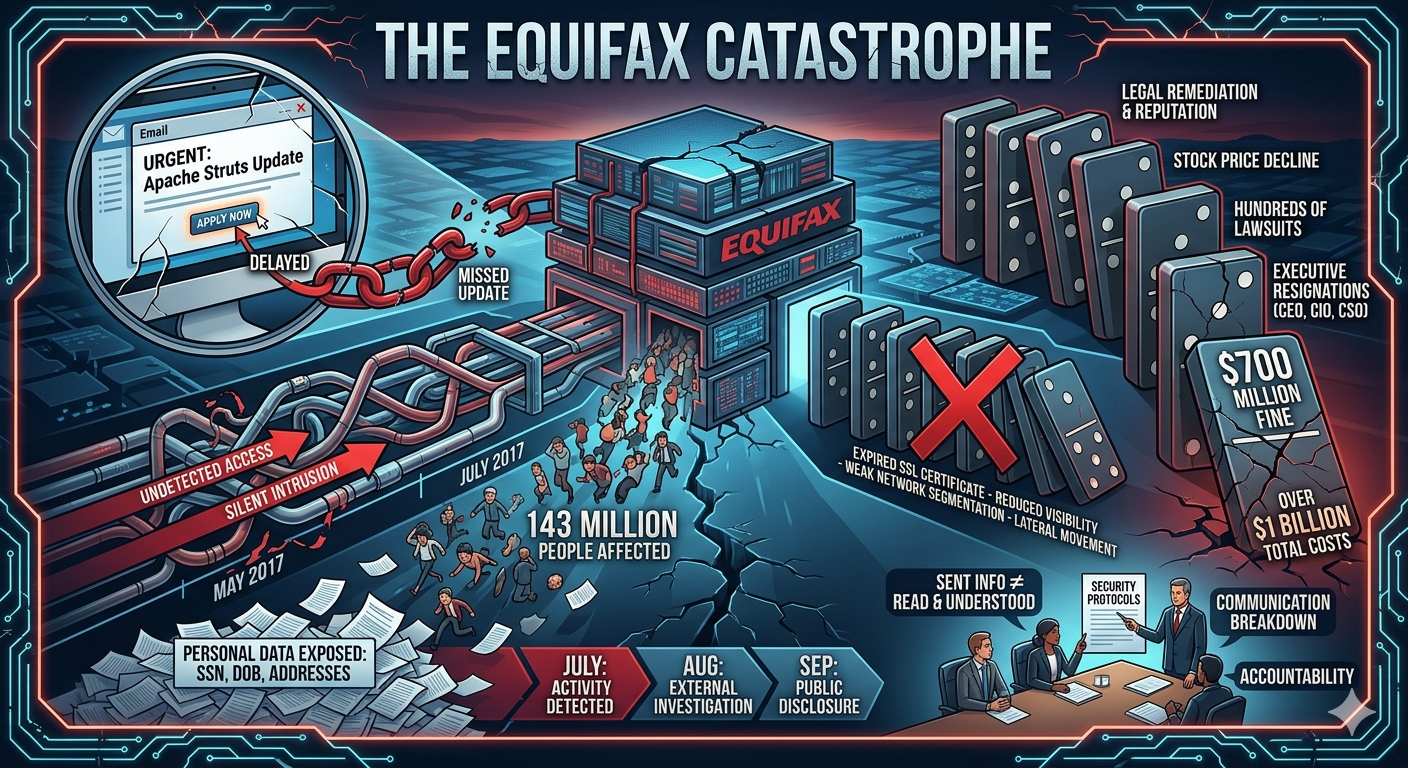
In May 2017, attackers exploited a known vulnerability in Apache Struts, a widely used web application framework.
A security patch had already been released—but it was never applied to a critical system.
That single missed update became the entry point.
How the breach unfolded
Once inside, attackers remained undetected for over two months.
Key events:
- May 2017: Initial breach through unpatched vulnerability
- July 2017: Suspicious activity detected; system taken offline
- August 2017: External cybersecurity firm brought in
- September 2017: Public disclosure released
By then, the damage was already done.
Are your policies read on time and by the right people?
DocRead makes compliance simple
What was exposed
The breach affected approximately 143 million people, exposing:
- Names
- Social Security numbers
- Birth dates
- Addresses
- Driver’s license numbers
Additional exposure included:
- Credit card data (~209,000 users)
- Dispute documents (~182,000 users)
- Data from UK and Canadian individuals
Why it became so severe
This was not a zero-day attack or unknown exploit. It was a known vulnerability with a known fix.
But multiple failures compounded the issue:
- A missed security patch left systems exposed
- An expired SSL certificate reduced monitoring visibility
- Weak network segmentation allowed lateral movement
- Slow data exfiltration delayed detection
- Public disclosure was delayed after discovery
The result: attackers operated inside Equifax systems undetected for weeks.
The impact
The consequences were significant:
- Up to $700 million settlement with regulators
- Over $1 billion in total costs (legal, remediation, reputation)
- Hundreds of lawsuits filed
- Significant stock price decline
- Executive resignations, including the CEO, CIO, and CSO
The core lesson
The Equifax breach is often framed as a cybersecurity incident. But at its core, it was much simpler:
A known patch existed.
It was not applied.
And “later” became a two-month silent intrusion into one of the world’s most sensitive data systems.
How DocRead helps reduce this risk
The Equifax incident wasn’t only a technical failure—it was also a breakdown in communication, accountability, and follow-through.
DocRead helps address this gap in Microsoft 365 and SharePoint by ensuring critical updates, policies, and compliance documents are:
- Distributed properly
- Acknowledged by employees
- Tracked with audit visibility
Because sending information is not enough—organizations need proof it was read and understood.
Final thought
Most major breaches don’t start with sophisticated attacks. They start with small oversights: a missed update, an unverified assumption, or a delayed action.
Equifax is a reminder that in cybersecurity, “later” can become the most expensive decision an organization ever makes.
Get your free Standard Operating Procedures guide
Creating Standard Operating Procedures for your organisation doesn't have to be complicated. This guide will introduce you to the whole lifecycle from creation to training and distribution.
You may also like:
April 24, 2026
April 17, 2026
The Difference Between Governance Infrastructure and Governance Theater Most organizations don’t lack governance. They ...
April 10, 2026
The Difference Between Governance Infrastructure and Governance Theater Most organizations don’t lack governance. They ...
April 3, 2026
Cost Reduction Is a Leadership Skill Cost reduction is usually framed as a finance ...
March 27, 2026
Cost Reduction Is a Leadership Skill Cost reduction is usually framed as a finance ...
March 13, 2026
Cost Reduction Is a Leadership Skill Cost reduction is usually framed as a finance ...